My server was hacked. ToT
One day i found that i couldn’t login the server thru SSH and the CPU usage jumped to 100% for more than 12 hours. Finally i could login as root and found that a new user R00T was created and the SSH service was restarted with all settings in the sshd config file commented out. =.=
So from now on i will use Key Authentication instead of simple Password Authentication. Here is a very useful guide on Linode.com which shows you how to secure your server.
Linode Library – Securing Your Server
In order to use the Key Authentication, you need to generate the private key and public key on your desktop/labtop computers. This is straight forward if you are a Mac or Linux user who could use the ssh-keygen command. But for Windows user, you have to use 3rd party program like PuTTYgen. I suggest using WinSCP + PuTTY.
1. Download and install WinSCP, the puttygen.exe and pageant.exe are bundled.
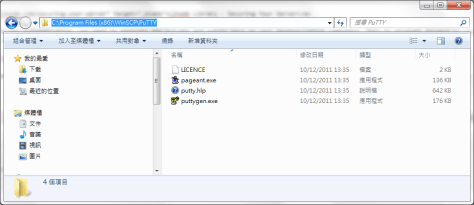
2. Also download the putty.exe.
3. Run puttygen.exe and click the Generate button. Move your mouse around the desktop until the key is generated.

4. Enter the Key passphrase and save the private key as id_rsa.ppk.
5. Login to the server, create the /home/<user>/.ssh folder.
6. Create the /home/<user>/.ssh/authorized_keys on the server. Copy the public key from the puttygen.exe window and paste it to the newly created authorized_keys file. Make sure is it on ONE LINE.

7. Modify the file owner and permission.
chown -R <user>:<user> /home/<user>/.ssh chmod 700 /home/<user>/.ssh chmod 600 /home/<user>/.ssh/authorized_keys
8. Change the following 2 settings in /etc/ssh/sshd_config as follow.
PasswordAuthentication no PermitRootLogin no
9. Restart the SSH service
/etc/init.d/ssh restart
10. Run pageant.exe and add the private key.
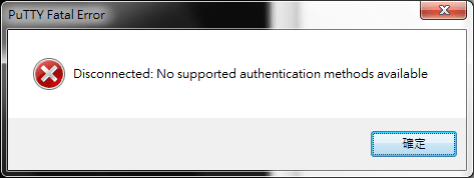
11. The Key Authentication is now working. If you do not add the private key in the pageant.exe. You will get the following error.
Now you only need to worry how to keep your client machines safe from being stolen.
Done =)
Reference:

